It is my Birthday
- Description: I sent out 2 invitations to all of my friends for my birthday! I'll know if they get stolen because the 2 invites look similar, and they even have the same md5 hash, but they are slightly different! You wouldn't believe how long it took me to find a collision. Anyway, see if you're invited by submitting 2 PDFs to my website.
- Difficulty: Medium
🔎 Solution
From the challenge description, it is clear that this task revolves around an MD5 hash collision - a scenario where 2 different inputs produce the same MD5 hash value. A similar idea also appears in picoCTF with the challenge Apriti sesamo, which exploits a SHA-1 hash collision instead.
In this case, I generated 2 different files that share the same MD5 hash using the fastcoll tool. The tool can be downloaded and built with the following commands:
git clone https://github.com/upbit/clone-fastcoll fastcoll
cd fastcoll
make
After that, I generated 2 colliding files using:
./fastcoll/fastcoll md5_data
The output consists of 2 files, md5_data1 and md5_data2.
When checking their MD5 hashes, both files produce exactly the same hash value:
> md5sum md5_data*
6ce6291e2a8497d0b25b3c553f1f4444 md5_data1
6ce6291e2a8497d0b25b3c553f1f4444 md5_data2
However, comparing their contents shows that the 2 files are clearly different. This confirms that they satisfy the condition of an MD5 hash collision:
> diff md5_data1 md5_data2
1,2c1,2
< �Y�9�1����iBZ,�CI�/O���#)����Iţ�� u9�ê���XBGC�h�k���w�
��L�MϽ?▒�M^�*<ə�h��|�n��%�ڧ^d
\ No newline at end of file
---
> �Y�9�1����iBZ,;CI�/O���#)����Iţ�� u9�C����XBGC�h�����w�
��L�MϽ?▒�M^�*<ə����|�n��%�Z�^d
\ No newline at end of file
Since the web application only accepts PDF uploads, I simply appended the .pdf extension to both files and uploaded them to the site.
This successfully triggered the vulnerability and returned the flag.
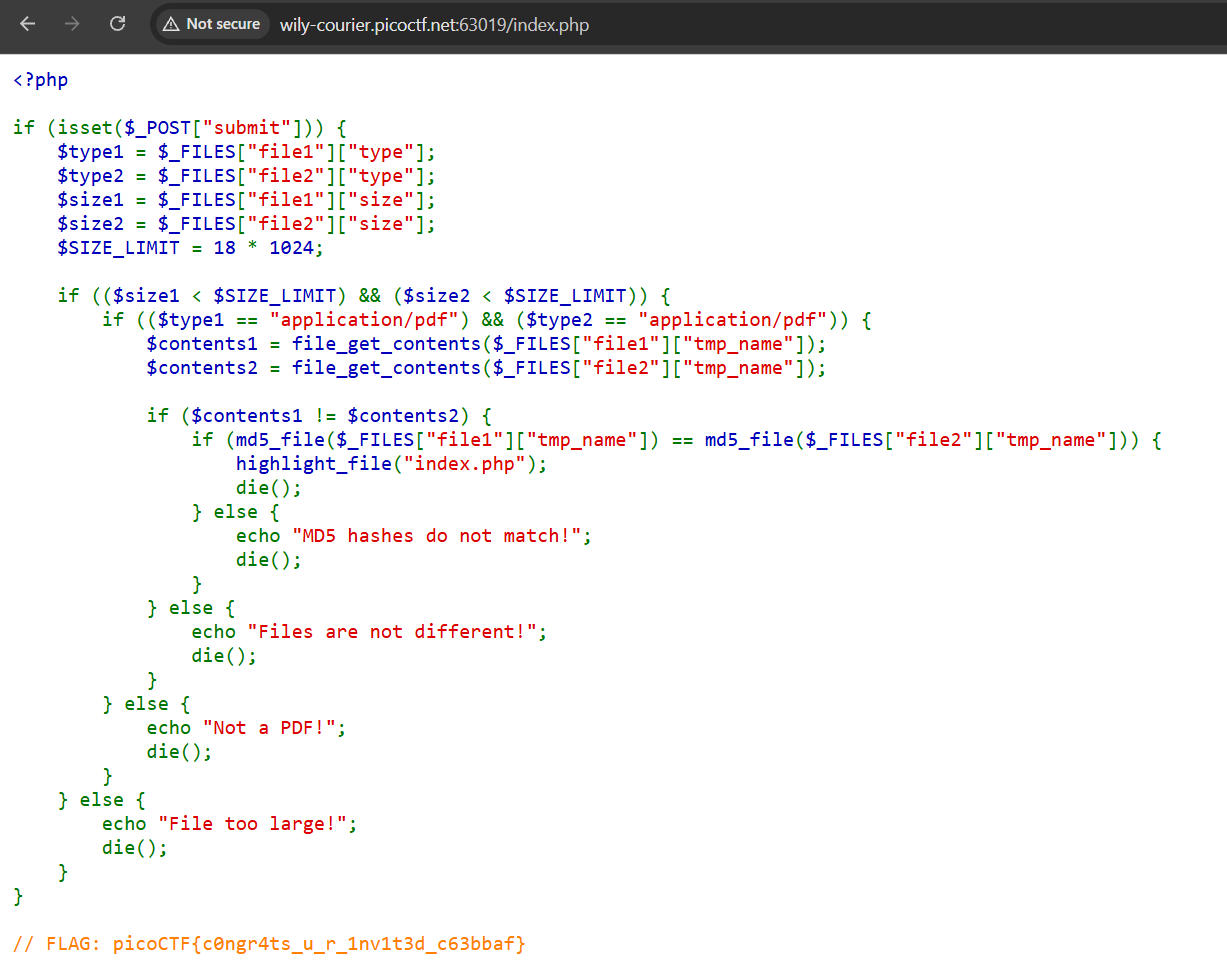
🚩Flag
picoCTF{c0ngr4ts_u_r_1nv1t3d_c63bbaf}